OIDC step-up authentication
This use case shows how to enforce step-up authentication using OpenID Connect (OIDC) with Airlock Microgateway. Step-up is a general authentication concept: it raises the required authentication strength for selected actions or paths. Airlock Microgateway currently supports interactive authentication via OIDC, so this article describes how to implement step-up requirements based on OIDC authentication results (e.g., required scopes and ACR values).
The configuration steps below show how to configure an access control policy that enforces OIDC authentication for an application path and adds step-up requirements for selected subpaths. The examples are based on a Microsoft Entra ID integration and must be adjusted to your setup.
Do not confuse this feature with OAuth 2.0 step-up as described in RFC 9470.
- RFC 9470 defines step-up for OAuth 2.0, while this Microgateway implementation applies step-up requirements in the context of OIDC-based authentication (evaluating OIDC authentication results such as scopes and ACR values).
Prerequisites
- A Gateway deployment.
- Session handling must be configured.
- An
HTTPRouterouting traffic to your application. - A working OIDC setup as described in the OIDC authentication use case (
JWKS,OIDCProvider,OIDCRelyingParty,AccessControlPolicywith OIDC authentication). - An OIDC provider setup with issuer, client ID, client secret, and the required endpoints.
Note: The OIDC provider configuration is not part of this article.
Configuration
This section shows how to configure Airlock Microgateway with an access control policy that first enforces OIDC authentication for an application path and then adds step-up requirements for selected subpaths.
Create a baseline AccessControlPolicy resource
Start with a simple policy that requires OIDC authentication for /app/ and denies all other requests.
Add step-up requirements
- Extend the
AccessControlPolicywith step-up requirements: /app/confidential/requires the scope confidential./app/confidential/admin/additionally requires a stronger authentication level indicated by an allowed ACR value (example values:urn:your-company:acr:weakorurn:your-company:acr:strong).
- Configure step-up requirements in
authorization.ensured.oidc: ensured.oidc.scopes(required scopes)ensured.oidc.acrInValues(allowed ACR values)
- Define policies from most restrictive to least restrictive, so that more specific paths are matched first.
Validation
Validate step-up in a browser
Attempt to access endpoints behind the targeted HTTPRoute. If the configuration is correct, the following will be observed:
- Accessing
/app/triggers OIDC authentication (if the user is not authenticated). - Accessing
/app/confidential/requires the scope confidential according to the policy. - Accessing
/app/confidential/admin/requires the scope confidential and one of the configured ACR values. - If authorization succeeds, the request is forwarded to the back-end.
Validate step-up in Grafana
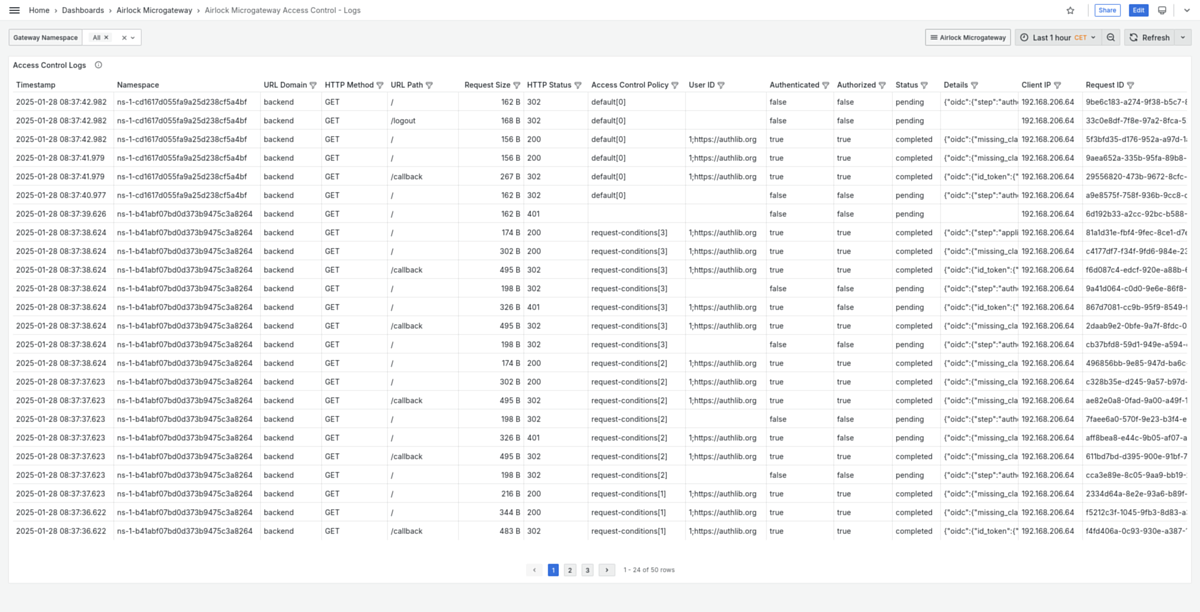
The built-in Grafana dashboard Airlock Microgateway Access Control - Logs provides step-up relevant details per request.
- Look at the Details column. It contains an OIDC-related JSON structure; the field
.oidc.stepcategorizes the request within the OIDC flow.
For an OIDC flow with step-up, you typically observe the following.oidc.stepvalues: authentication-redirectauthorization-grant-exchangeapplication-accessstep-up-redirectauthorization-grant-exchangeapplication-access
- Use this values to verify that:
- the initial access triggers authentication and then application access, and
- accessing a step-up protected area triggers an additional step-up-redirect followed by another token exchange and application access.