OIDC authentication
This use case shows how to enforce authentication with Airlock Microgateway to allow access only to authenticated and authorized users. Access is granted based on access policies evaluating the claims in the ID token provided by an external OIDC provider.
The configuration steps below show how to configure authentication enforcement with OIDC to protect a web application. The examples are based on a Microsoft Entra ID integration and must be adjusted to your setup.
Prerequisites
- A Gateway deployment.
- Session handling must be configured.
- An
HTTPRouteroutes traffic to your application. - An OIDC provider setup with issuer, client ID, client secret, and the required endpoints.
Note: The OIDC provider configuration is not part of this article.
Configuration
This section shows how to configure Airlock Microgateway with an access control policy using OIDC.
Create a JWKS resource
Create a JWKS to instruct Microgateway where to fetch the provider’s public signing keys for ID token signature verification.
Create an OIDCProvider resource
Create an OIDCProvider that defines the trusted issuer with the required endpoints, and references the JWKS for ID token signature verification.
Ensure that the logoutPath and redirectPath within the OIDCRelyingParty fulfill the following constraints:
RedirectPath:
Ensure this path is matched by theHTTPRouteto which the referencingAccessControlPolicyis attached.LogoutPath:- Ensure this path is matched by the
HTTPRouteto which the referencingAccessControlPolicyis attached. - If the policy referencing this
OIDCRelyingPartyhas a request condition, you must ensure that it also matches these logout requests.
- Ensure this path is matched by the
Otherwise, the OIDC callback/logout requests may not work.
Example
Create a client secret
Create a Kubernetes Secret that contains the OIDC client secret under the key client.secret. The OIDCRelyingParty references this secret by name.
Create an OIDCRelyingParty resource
Create a OIDCRelyingParty that links Microgateway to the client registration at the OIDC provider. The following settings might change based on your environment: clientID, clientSecretRef, scopes, redirectPath and logoutPath.
Create an AccessControlPolicy resource
Create a AccessControlPolicy that targets your HTTPRoute, triggers OIDC authentication via the relying party, and applies access policy rules.
About AccessControlPolicy configurations:
- Multiple policies can be configured. The
requestConditionswork as a policy selector. - The list of policies is processed from top to bottom – the first matching policy will be applied.
- When multiple policies are configured, all policies must have
requestConditionsexcept the last one which works as a fallback policy. Otherwise, a validation error will appear. - If only a single policy is configured,
requestConditionsmust not be set and an additional fallback policy is not required. - An empty authorization object value
{}disables autorization and grants access to the backend whiledeny: {}rejects the requests. - A mix of
requireAllandrequireAnyauthorization definition is not supported. - When accessing the
logoutPath, the user is logged out from the OIDC relying party. If required, log-out from the OIDC provider must be triggered separately.
Validation
Validate the OIDC flow in a browser
Attempt to access an endpoint behind the targeted HTTPRoute. If the configuration is correct, the following occurs:
- You are redirected to the OIDC provider for login.
- After successful authentication, the provider redirects back to the configured callback path (e.g.,
/callback). - Microgateway validates the ID token signature and issuer using the configured JWKS and authorizes the request according to the policy.
- The request is forwarded to the back-end.
If authentication succeeds but authorization fails, verify that the expected claim is present in the ID token and that your matcher value matches the claim value.
Validate OIDC in Grafana
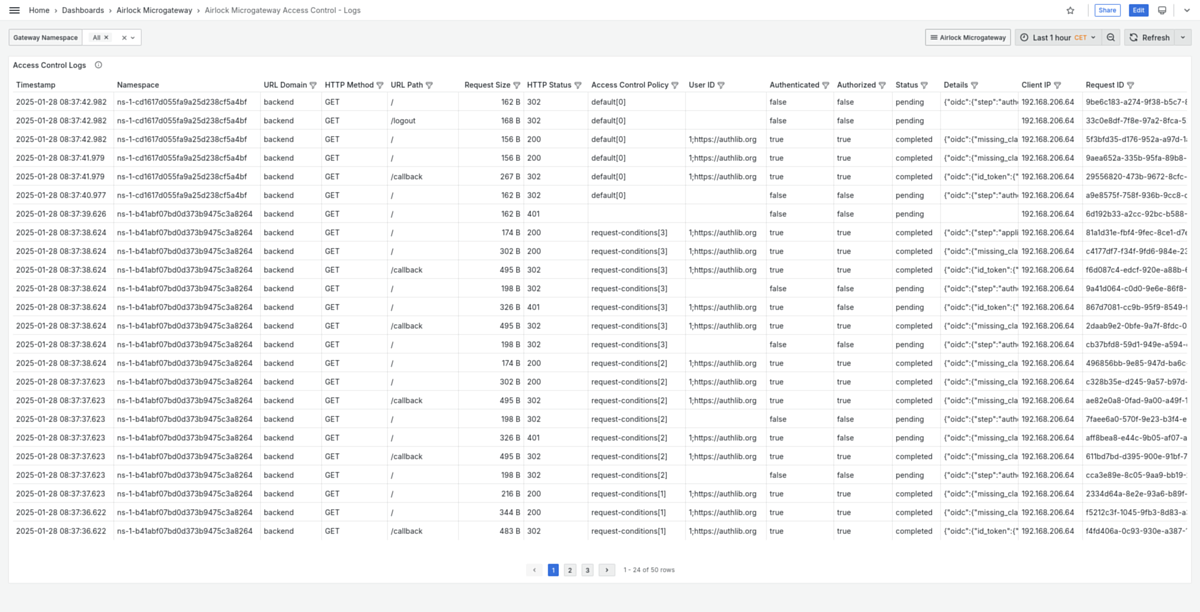
The built-in Grafana dashboard Airlock Microgateway Access Control - Logs shows log information for requests with access control details available.