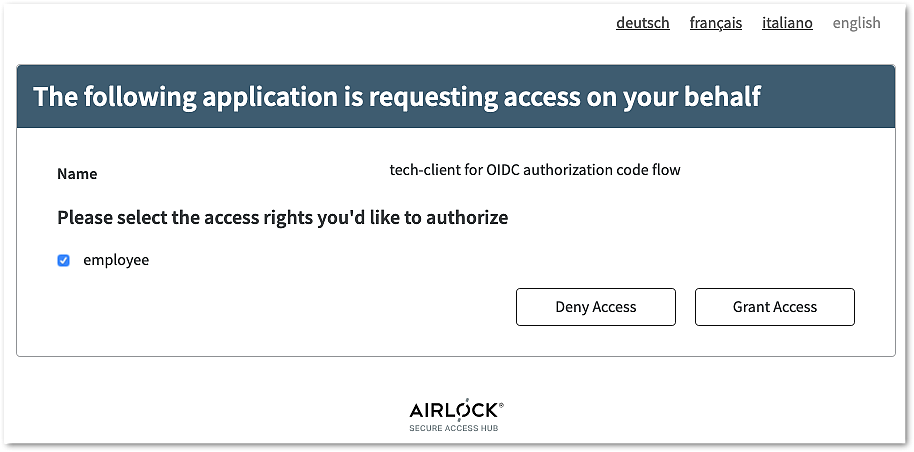
If both authentication and consent grants have succeeded, Airlock IAM redirects the browser to the redirect_uri requested in Step 1.
Redirect URL after starting hybrid code flow and authentication
https://oidc.airlock.com/application/demo# code=xRbH9uoaMMWB6urmWsg8b1xwJQF~JfD2s9CoUvwVWX42YxBwqfeC2RVWeG1HkvkdtxHz
&id_token=eyJ0...Zxo
&access_token=YL3x...ytP
&token_type=bearer
&expires_in=1234
&state=ee26b0dd4a...28a8ffCompared to the OIDC authorization code flow, an additional ID token and access token are sent to the browser directly with the authorization code.
The code and the tokens are passed as a fragment rather than a query string (using # instead of ? in the URL). This is because the ID and access tokens are meant to be extracted by the web browser (or mobile app) and should not be sent to the RP (client).
Using a fragment (#) is the default behavior.
The Airlock IAM configuration allows changing the default to send the tokens and the code as query or form post parameters. This may be required user agent or the relying party.
See Advanced Settings in the hybrid flow configuration for further information.
The browser (or mobile app) may now examine and use the ID and access token and then sends the authorization code to the RP (client).