The Authorization Code Grant is usually used to delegate authorization from one web application to another.
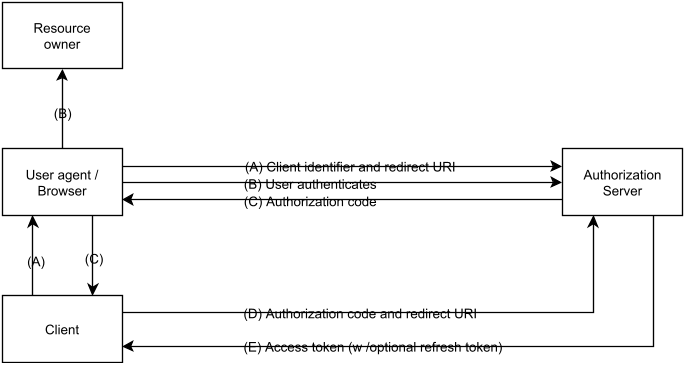
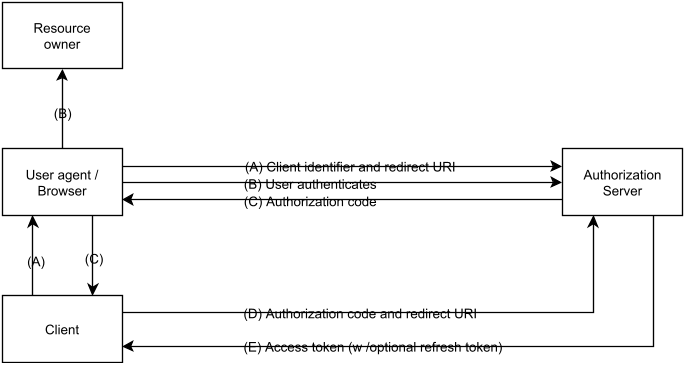
The OAuth 2.0 RFC depicts the Authorization Code Grant as follows:
- Example:
Goal: Use Facebook as an Authorization Server to authorize access to pictures to Pinterest (Client).
- The user (Resource Owner) navigates in her browser (User-Agent) to Pinterest (Client). Pinterest would like to display pictures contained in the user's Facebook account.
This step is not part of the Authorization Code Grant. - (A) Pinterest (client) opens a browser window for the user. The URL points to Facebook (Authorization Server), with a request saying that Pinterest (client_id) would like to access the user's pictures (scope). This request contains a redirect URL.
- (B) The user authenticates with Facebook and is asked if she would like to grant Pinterest access to her pictures (consent). We assume the user grants access.
- (C) Facebook instructs the browser to redirect to the client (this is the redirect URL from step 2). This redirect also contains the Authorization Code. The browser window is now closed and control is back with the client (Pinterest)
- (D) Pinterest makes an authenticated REST call (client authentication) to Facebook (authorization server) to exchange the Authorization Code for an Access Token (E).
- Finally, Pinterest uses the Access Token to access the user's Facebook pictures.