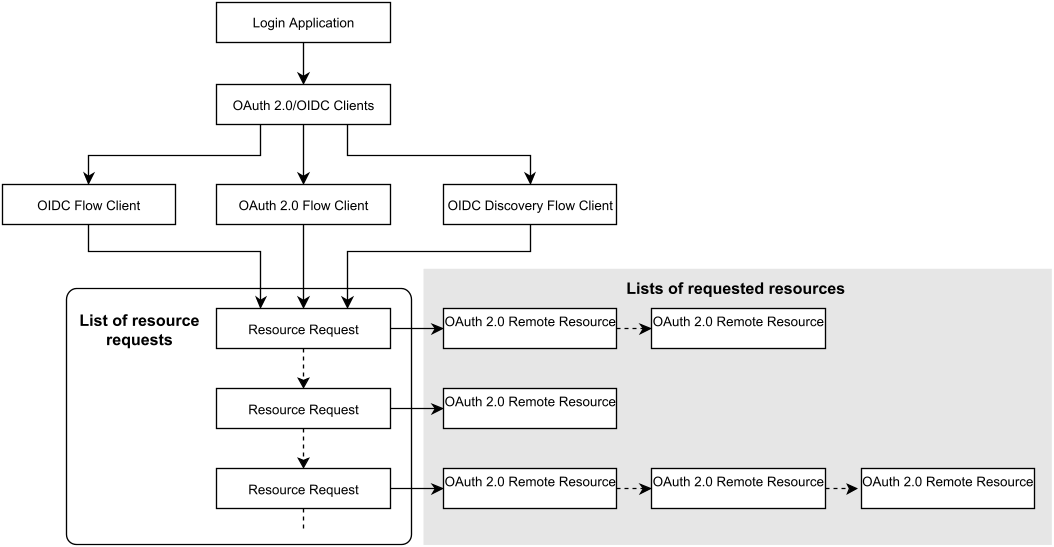
When using IAM as OAuth or OIDC client, it is possible to use the OAuth 2.0/OIDC configuration to collect claims (i.e., information about the user) from different resources.
In this context, the term resource refers to sources of claims and should not be confused with the Resource Server defined in OIDC.
- Possible sources of claims are:
- ID token
- Remote service endpoints (e.g.,
userinfoendpoint)
- Possible types of claims are:
- User identities (
username,sub,issuer,aud, etc.) - Roles
- Context data
- Information related to authentication and authorization (ACR values, scopes, etc.)
- Technical information (validity, etc)