OAuth 2.0 specifies four grant types. We only discuss the Authorization Code Grant and the Implicit Grant, as they are the most common and Airlock IAM supports both. We give a brief overview of these grants in order to illustrate their most common use case. The Terms and definitions below explains some OAuth 2.0 terms in more detail.
Overview: Authorization Code Grant
The Authorization Code Grant is usually used to delegate authorization from one web application to another.
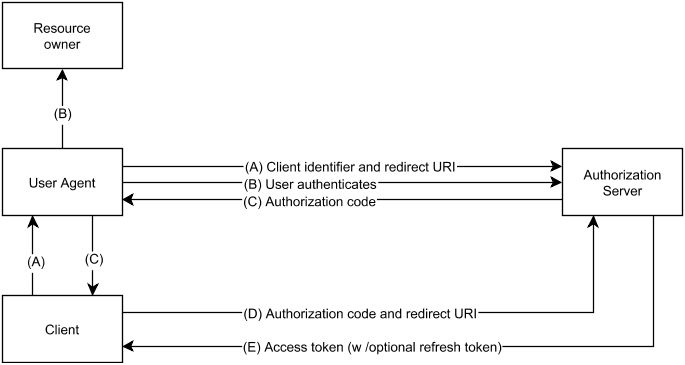
The OAuth 2.0 RFC depicts the Authorization Code Grant as follows:
We give an example to illustrate this grant type.
Goal:
Delegate authorization to access Facebook (Authorization Server) pictures to Pinterest (Client).
- The user (Resource Owner) navigates in her browser (User-Agent) to Pinterest (Client). Pinterest would like to display pictures contained in the user's Facebook account.
- (A) Pinterest redirects the user to Facebook (Authorization Server), with a request saying that Pinterest (client_id) would like to access the user's pictures (scope).
- (B) The user authenticates with Facebook and is asked if she would like to grant Pinterest access to her pictures. We assume the user grants access.
- (C) Facebook sends a redirect containing an Authorization Code to Pinterest.
- (D) Pinterest directly authenticates with Facebook and then uses the Authorization Code to obtain an Access Token (E).
Finally, Pinterest uses the Access Token to access the user's Facebook pictures.
Overview: Client Credentials Grant
The client credentials grant is used by clients to directly obtain an access token with the client's credentials and without a user's involvement.
To use the client credentials grant, follow these steps:
- The client sends a request to the authorization server.
- The server verifies the credentials supplied in the request.
- Upon success, the authorization server issues an access token and sends it to the client in the response.