Use Case Scenario
This use case demonstrates the different steps required to execute an authorization code flow with user interactions.
This use case demonstrates the different steps required to execute an authorization code flow with user interactions.
The client is already registered through dynamic client registration (AS-centric AS - client credentials grant usage example) or configured as a static client in the configuration (OAuth AS configuration - AS-centric
To start the authorization code flow, open a browser window and enter the following URL:
Browser URL to start an authorization code flow
https://oidc.airlock.com/auth-login/oauth2/v3/myAS/authorize?response_type=code&redirect_uri=https://oidc.airlock.com/application/demo&client_id=oidc-client&state=ee26b0dd4a...28a8ff&scope=employee%20openid
To successfully start an authorization code flow, the following conditions must be met:
If one of the conditions is not met, the authorization server will return an error message in the browser.
Submitting the "state" parameter is not required by the standard, but it is strongly recommended to protect against CSRF.
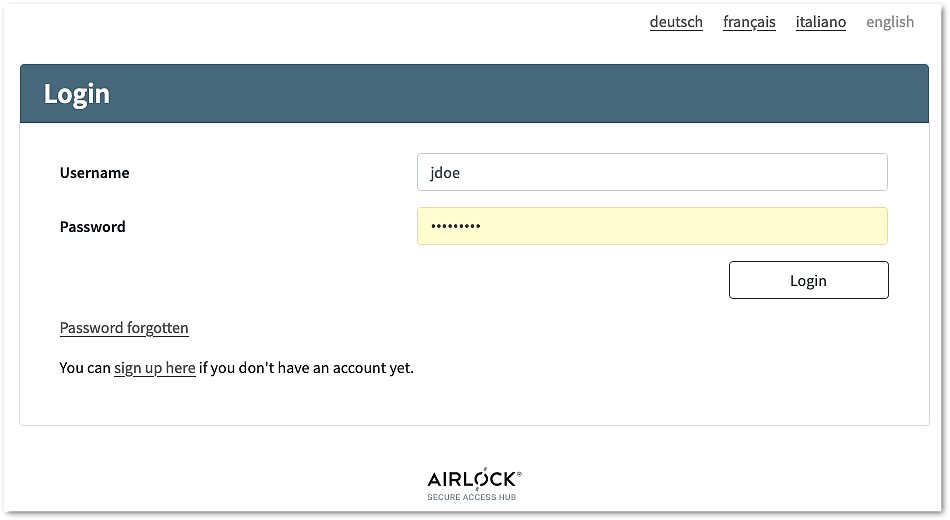
Airlock IAM will present a login screen:
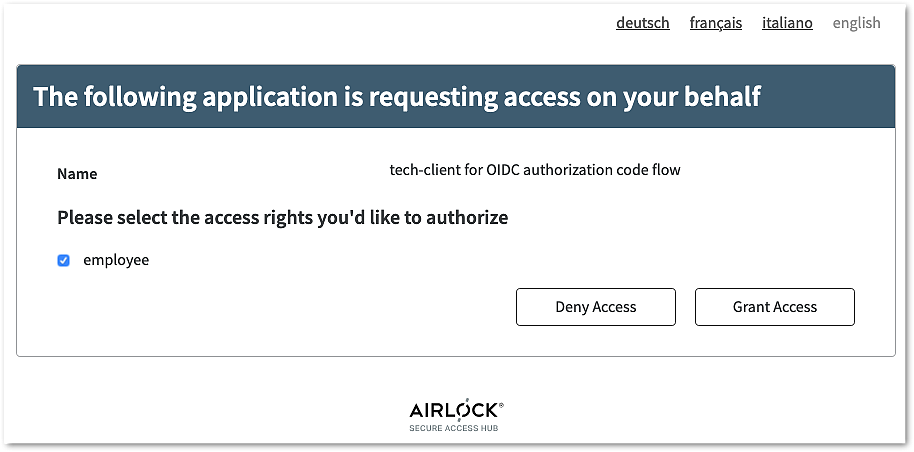
... and optionally ask for consent:
If both authentication and consent grants have succeeded, Airlock IAM will redirect the browser to the redirect_uri requested in step 1.
Code Block Redirect URL in response to authorization code flow
https://oidc.airlock.com/application/demo?code=xRbH9uoaMMWB6urmWsg8b1xwJQF~JfD2s9CoUvwVWX42YxBwqfeC2RVWeG1HkvkdtxHz&state=ee26b0dd4a...28a8ff
The code provided in the redirect URL is called an authorization code.
Now follows a request to the token endpoint of the authorization server to exchange the authorization code for access, refresh, and optionally ID token.
token endpoint request
https://oidc.airlock.com/auth-login/rest/oauth2/authorization-servers/myAS/token
Content-Type: application/x-www-form-urlencoded
Authorization: Basic dXNlcm5hbWU6cGFzc3dvcmQ
grant_type=authorization_code
code=RSEzh6Ay3rCuCXY5znRBeY2Z5Fb%7EyHCbrg17CdEcdQMxy76pgbdXvM1dJBkFfnxMNiEy
redirect_uri=https://oidc.airlock.com/application/demo
It is recommended to configure the authorization server, to enforce authentication on the token endpoint.
The authorization server will respond as follows:
Code Block token endpoint response
200 OK
{
"access_token": "eyJraWQiOiI3YWRmMz...E9nfs7YyJZdRFP",
"scope": "email",
"id_token": "eyJraWQiOiI3YWRmMzgp74...Ex86vUkyMGqxQg",
"token_type": "bearer",
"expires_in": 17999
}